- Topic1/3
42k Popularity
30k Popularity
46k Popularity
9k Popularity
21k Popularity
- Pin
- 🎉 The #CandyDrop Futures Challenge is live — join now to share a 6 BTC prize pool!
📢 Post your futures trading experience on Gate Square with the event hashtag — $25 × 20 rewards are waiting!
🎁 $500 in futures trial vouchers up for grabs — 20 standout posts will win!
📅 Event Period: August 1, 2025, 15:00 – August 15, 2025, 19:00 (UTC+8)
👉 Event Link: https://www.gate.com/candy-drop/detail/BTC-98
Dare to trade. Dare to win.
- 🎉 Gate Square Growth Points Summer Lucky Draw Round 1️⃣ 2️⃣ Is Live!
🎁 Prize pool over $10,000! Win Huawei Mate Tri-fold Phone, F1 Red Bull Racing Car Model, exclusive Gate merch, popular tokens & more!
Try your luck now 👉 https://www.gate.com/activities/pointprize?now_period=12
How to earn Growth Points fast?
1️⃣ Go to [Square], tap the icon next to your avatar to enter [Community Center]
2️⃣ Complete daily tasks like posting, commenting, liking, and chatting to earn points
100% chance to win — prizes guaranteed! Come and draw now!
Event ends: August 9, 16:00 UTC
More details: https://www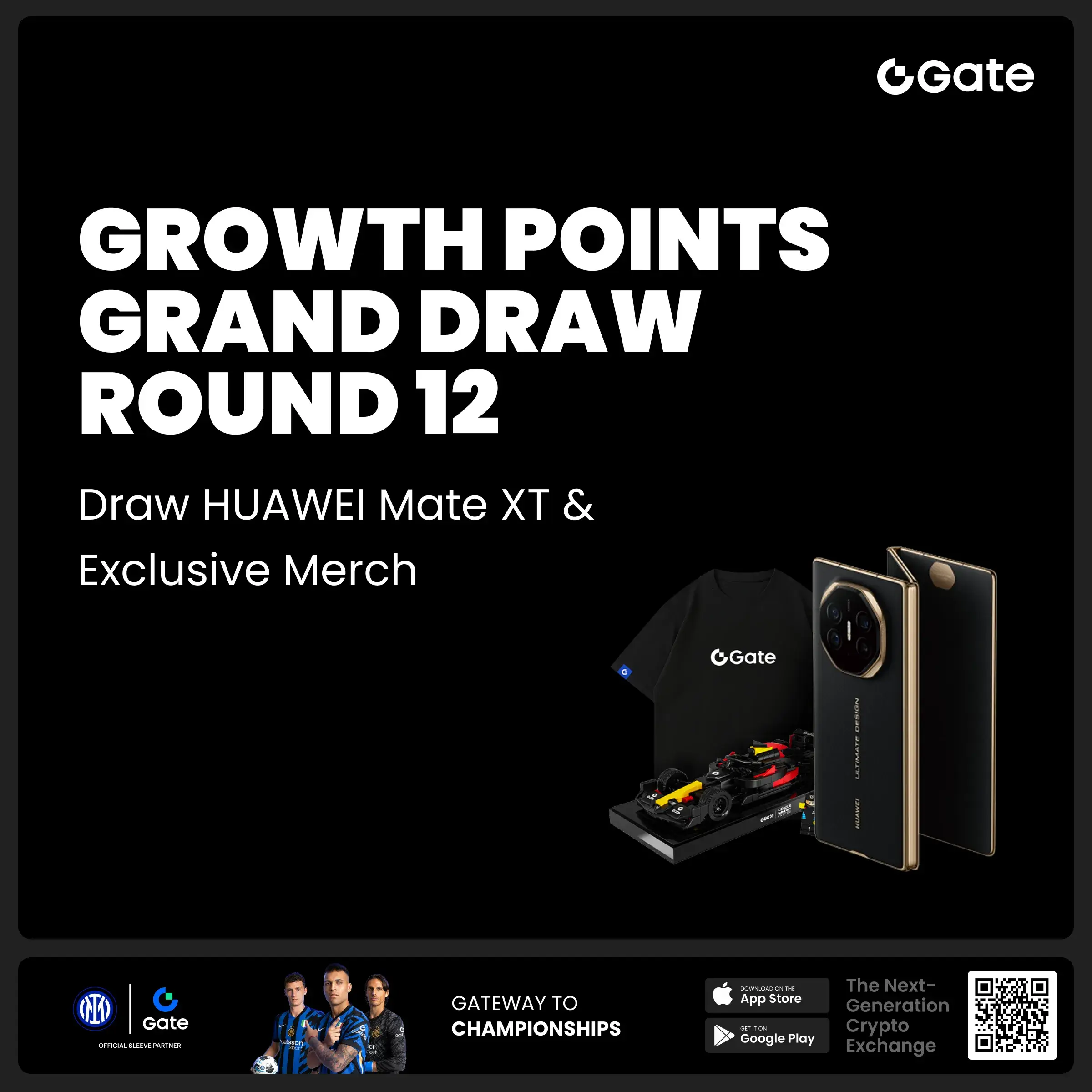
The United Nations report reveals that the Lazarus Group laundered $147.5 million in 2023.
Recently, a joint internal report revealed the latest activities of the North Korean hacker group Lazarus Group. It is reported that after stealing funds from a digital asset exchange last year, the organization laundered $147.5 million using a virtual money platform in March this year.
The United Nations Security Council Sanctions Committee's monitors are investigating 97 suspected cyber attacks by North Korean hackers targeting cryptocurrency companies that occurred between 2017 and 2024, involving amounts as high as $3.6 billion. This includes an attack on a certain cryptocurrency exchange at the end of last year, which resulted in a loss of $147.5 million, followed by the completion of the money laundering process in March this year.
In 2022, the United States imposed sanctions on the virtual money platform. The following year, two co-founders of the platform were accused of assisting in laundering over $1 billion, including transactions with the North Korean cybercrime organization Lazarus Group.
According to research by experts in digital currency investigations, the Lazarus Group converted $200 million worth of cryptocurrency into fiat currency between August 2020 and October 2023.
The Lazarus Group has long been considered a major perpetrator of large-scale cyber attacks and financial crimes globally. Their targets span multiple sectors, including banking systems, cryptocurrency exchanges, government agencies, and private enterprises. The following will delve into several typical cases, analyzing how the Lazarus Group successfully implements these astonishing attacks through its complex strategies and technical means.
Lazarus Group's social engineering and phishing attacks
According to European media reports, Lazarus has targeted military and aerospace companies in Europe and the Middle East. They posted fake job advertisements on social media platforms to lure employees into downloading PDF documents containing malicious executable files, thus conducting phishing attacks.
This type of social engineering and phishing attack aims to exploit psychological manipulation to lure victims into lowering their guard and performing dangerous actions such as clicking on links or downloading files, thereby jeopardizing system security.
Their malware can exploit vulnerabilities in the victim's system to steal sensitive information.
In a six-month attack against a certain cryptocurrency payment provider, Lazarus employed a similar approach. They sent fake job offers to engineers while launching technical attacks such as distributed denial of service, and attempted to brute force passwords, ultimately resulting in a loss of $37 million for the provider.
Multiple incidents of attacks on cryptocurrency exchanges
On August 24, 2020, a wallet of a certain cryptocurrency exchange in Canada was hacked.
On September 11, 2020, due to the leak of a private key, unauthorized transfers amounting to $400,000 occurred in multiple wallets controlled by a certain project team.
On October 6, 2020, a certain cryptocurrency exchange unauthorizedly transferred $750,000 worth of digital assets from its hot wallet due to a security vulnerability.
The funds from these attack incidents were pooled into the same address in early 2021. Subsequently, the attackers sent the stolen funds to certain withdrawal addresses through multiple transfers and exchanges.
The founder of a certain mutual insurance platform was attacked by a Hacker.
On December 14, 2020, the personal account of the founder of a mutual insurance platform was hacked, resulting in the theft of 370,000 NXM (approximately 8.3 million USD).
The stolen funds were transferred between multiple addresses and exchanged for other assets. The Lazarus Group conducted operations such as fund obfuscation, dispersion, and aggregation through these addresses. Some of the funds were cross-chain transferred to the Bitcoin network, then back to the Ethereum network, and finally obfuscated through a mixing platform before being sent to the withdrawal platform.
From December 16 to 20, 2020, one of the involved addresses sent over 2500ETH to a certain mixing platform. A few hours later, another related address began withdrawal operations.
The hacker transferred part of the funds to the withdrawal address used in the previous incident through multiple transfers and exchanges.
From May to July 2021, the attacker transferred 11 million USDT to a certain exchange deposit address.
From February to March and from April to June 2023, the attacker sent 2.77 million USDT and 8.4 million USDT to different withdrawal platform deposit addresses through intermediary addresses.
Latest Attack Incident Analysis
In August 2023, in two separate hacker attack incidents, 624 and 900 stolen ETH were transferred to a certain mixing platform.
After transferring ETH to the mixing platform, the funds were immediately withdrawn to multiple new addresses. On October 12, 2023, the funds from these addresses were again consolidated and transferred to a new address.
In November 2023, this address began transferring funds, eventually sending the funds to the deposit addresses of multiple withdrawal platforms through intermediaries and exchanges.
Summary
The Lazarus Group primarily obfuscates funds after stealing digital assets through cross-chain operations and the use of mixers. After obfuscation, they withdraw the stolen assets to target addresses and send them to a fixed group of addresses for withdrawal operations. The stolen digital assets are usually deposited into specific withdrawal platform deposit addresses and then exchanged for fiat currency through over-the-counter trading services.
In the face of the ongoing and large-scale attacks by the Lazarus Group, the Web3 industry is facing severe security challenges. All parties in the industry need to strengthen cooperation and continuously enhance security protection capabilities to respond to such complex cybercriminal activities.